Overview
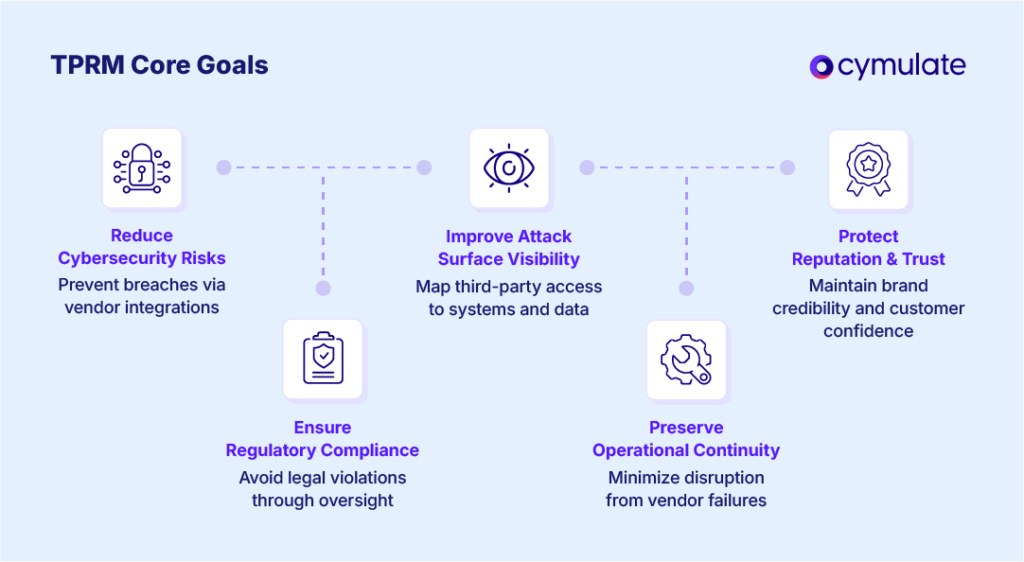
Vetting third-party plugins and integrations is a critical component of modern cybersecurity, especially as organizations increasingly rely on SaaS platforms, APIs, and marketplace apps to extend functionality. These tools can introduce significant risks—including data breaches, service disruptions, and compliance violations—if not properly assessed and managed. Below is a structured approach to vetting and securing third-party plugins and integrations, based on industry best practices and recent guidance.
Key Risks of Third-Party Plugins and Integrations
- Data Breaches: Vulnerabilities in third-party code can expose sensitive organizational or customer data.
- Malicious Plugins: Attackers may distribute plugins that mimic trusted tools (plugin squatting) to steal data or inject harmful content.
- Service Disruptions: Dependence on external services means outages or technical issues can directly impact business operations.
- Compliance Violations: Unvetted integrations may not meet regulatory requirements (e.g., PCI-DSS, GDPR), risking fines and reputational damage.
- Credential Exposure: Plugins with excessive permissions can leak API keys, tokens, or other credentials, leading to unauthorized access.
Best Practices for Vetting and Securing Third-Party Plugins
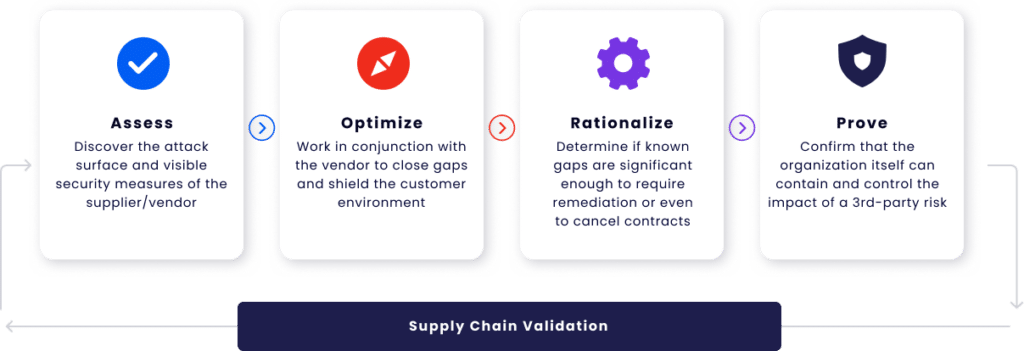
Pre-Integration Assessment
- Vendor Reputation: Research the plugin developer’s track record, support responsiveness, and update frequency. Abandoned or rarely updated plugins are higher risk.
- Security Reviews: Perform code reviews or request third-party security audits, especially for plugins with access to sensitive data.
- Least Privilege: Grant only the minimum permissions necessary for the plugin to function, reducing the potential impact of a compromise.
- Compliance Alignment: Ensure the plugin complies with relevant industry standards and organizational policies.
Integration and Deployment
- Approval Workflow: Implement a formal process for approving new integrations, including documentation and stakeholder sign-off.
- Isolation: Run third-party services in isolated environments with strict network controls to limit lateral movement in case of a breach.
- Ephemeral Credentials: Use short-lived, rotating credentials instead of long-term secrets to minimize exposure.
Ongoing Monitoring and Maintenance
- Continuous Monitoring: Use SaaS Security Posture Management (SSPM) tools or equivalent to track plugin activity, detect anomalies, and identify risky plugins.
- Regular Audits: Periodically review all integrated third-party services, revoking access for unused or redundant plugins.
- Update Management: Keep all plugins and integrations up to date with the latest security patches.
- Incident Response: Have a plan to quickly disable or remove compromised plugins and mitigate any damage.
Common Attack Scenarios and Mitigations
| Scenario | Description | Mitigation |
|---|---|---|
| Plugin Squatting | Malicious plugin mimics a trusted one to trick users into installation | Verify publisher identity, checksum, and download source |
| Data Injection | Plugin alters user input to generate harmful or inappropriate content | Input validation, output sanitization, and content moderation |
| Credential Theft | Compromised plugin leaks API keys or tokens | Use ephemeral credentials, principle of least privilege |
| Service Disruption | Third-party service outage impacts business operations | Choose reliable vendors, implement fallback mechanisms |
Tools and Processes
- SaaS Security Posture Management (SSPM): Platforms like Palo Alto Networks’ Strata Cloud Manager provide dashboards to review, filter, and manage third-party plugins across SaaS apps, highlighting unvetted or risky integrations.
- Automated Scanning: Deploy tools to scan for vulnerabilities or malicious behavior in third-party code.
- Logging and Analytics: Monitor API calls and user sessions to detect suspicious activity linked to third-party integrations.
Summary Table: Vetting Checklist
| Step | Action |
|---|---|
| Pre-Integration | Assess vendor reputation, request security audits, check compliance |
| Integration | Apply least privilege, isolate environments, use ephemeral credentials |
| Ongoing | Monitor activity, audit regularly, update promptly, have incident plan |
Conclusion
Vetting third-party plugins and integrations requires a combination of technical controls, governance processes, and continuous vigilance. By systematically assessing risks before integration, enforcing strict access controls, and maintaining ongoing oversight, organizations can significantly reduce their exposure to third-party-related security incidents.















Maple Ranking offers the highest quality website traffic services in Canada. We provide a variety of traffic services for our clients, including website traffic, desktop traffic, mobile traffic, Google traffic, search traffic, eCommerce traffic, YouTube traffic, and TikTok traffic. Our website boasts a 100% customer satisfaction rate, so you can confidently purchase large amounts of SEO traffic online. For just 720 PHP per month, you can immediately increase website traffic, improve SEO performance, and boost sales!
Having trouble choosing a traffic package? Contact us, and our staff will assist you.
Free consultation